lv ransomware | lv ransomware hacked lv ransomware In what can be described as a case of piracy among cybercrime gangs, the LV ransomware gang appears to have hijacked and modified the binary payload of the more infamous REvil group.
Canon LV-WX300ST 3D Ready DLP Projector - 720p - HDTV - 16:10 9880B002 . Visit the Canon Store. Currently unavailable. We don't know when or if this item will be back in stock. The Canon Lv-Wx300st Short Throw Multimedia Projector Will Fill A 5 .5 Foot Wide ; .
0 · lv ransomware hijackers
1 · lv ransomware hacked
2 · lv ransomware gang revil
3 · lv ransomware binary
Cleaning a Louis Vuitton Speedy Bag. Get a saddle soap, it will help remove any patina on your Louis Vuitton Speedy bag. You can use a damp cloth or baby wipes to remove stains. If ink stains your bag, you can remove that with a hairspray. Use a cleaning agent like Brasso or Wenol to restore the hardware of your bag.
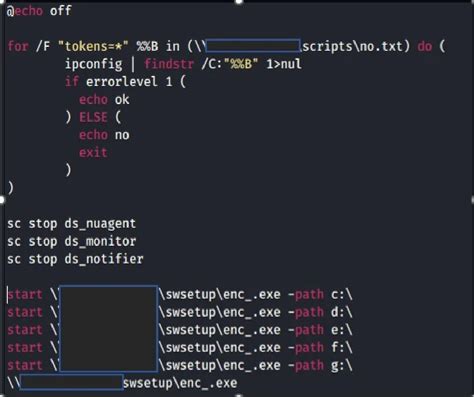
Oct 25, 2022 Researchers have discovered that the LV ransomware that has been in use since late 2020 is actually a modified version of the REvil ransomware binary that is being . The Trend Micro research team recently analyzed an infection related to the LV ransomware group, a ransomware as a service (RaaS) operation that has been active since late 2020, and is reportedly based on REvil (aka Sodinokibi).
CTU analysis revealed that the LV ransomware is not a distinct ransomware family; it is repurposed REvil ransomware. By modifying the binary of a prolific ransomware family, the GOLD NORTHFIELD threat actors significantly expedited their . Researchers have discovered that the LV ransomware that has been in use since late 2020 is actually a modified version of the REvil ransomware binary that is being distributed by a separate threat group. In what can be described as a case of piracy among cybercrime gangs, the LV ransomware gang appears to have hijacked and modified the binary payload of the more infamous REvil group.
German power electronics manufacturer Semikron has disclosed that it was hit by a ransomware attack that partially encrypted the company's network. Trend Micro provides a detailed analysis of an LV ransomware attack on a Jordan-based company, highlighting the attackers' methods and the wide range of targeted industries.
Researchers at Secureworks tracked what looked like a new ransomware strain, dubbed LV, which has been in the wild since late 2020, and found that it had identical code structure to REvil. In an incident, LV Ransomware compromised the corporate environment of a Jordan-based organization. It exploited the Microsoft flaws— ProxyShell and ProxyLogon —vulnerabilities and dropped a webshell in the public access folders.LV ransomware-as-a-service has been active since late 2020. The most recent infiltration entailed the compromise of the corporate environment of a Jordan-based entity, leveraging the double-extortion technique and exploiting ProxyShell flaws to extort potential targets. THREAT ADVISORY •ATTACK REPORT (Red) 2 | CVE Table CVE NAME PATCH CVE .
lv ransomware hijackers
New LV Ransomware Variant Hijacks Malicious Binaries Used by REvil Operators. The LV variant operators have been observed in the wild since October 2020, deploying a tweaked version of REvil’s binary with references to REvil’s C2 . The Trend Micro research team recently analyzed an infection related to the LV ransomware group, a ransomware as a service (RaaS) operation that has been active since late 2020, and is reportedly based on REvil (aka Sodinokibi). CTU analysis revealed that the LV ransomware is not a distinct ransomware family; it is repurposed REvil ransomware. By modifying the binary of a prolific ransomware family, the GOLD NORTHFIELD threat actors significantly expedited their . Researchers have discovered that the LV ransomware that has been in use since late 2020 is actually a modified version of the REvil ransomware binary that is being distributed by a separate threat group.
In what can be described as a case of piracy among cybercrime gangs, the LV ransomware gang appears to have hijacked and modified the binary payload of the more infamous REvil group. German power electronics manufacturer Semikron has disclosed that it was hit by a ransomware attack that partially encrypted the company's network.
Trend Micro provides a detailed analysis of an LV ransomware attack on a Jordan-based company, highlighting the attackers' methods and the wide range of targeted industries.
Researchers at Secureworks tracked what looked like a new ransomware strain, dubbed LV, which has been in the wild since late 2020, and found that it had identical code structure to REvil. In an incident, LV Ransomware compromised the corporate environment of a Jordan-based organization. It exploited the Microsoft flaws— ProxyShell and ProxyLogon —vulnerabilities and dropped a webshell in the public access folders.LV ransomware-as-a-service has been active since late 2020. The most recent infiltration entailed the compromise of the corporate environment of a Jordan-based entity, leveraging the double-extortion technique and exploiting ProxyShell flaws to extort potential targets. THREAT ADVISORY •ATTACK REPORT (Red) 2 | CVE Table CVE NAME PATCH CVE .
lv ransomware hacked

price of louis vuitton
women's lv
Think of it as a cheat sheet to help you tackle the candy-filled challenges. From clever combos to special moves, I spill all the secrets to help you crush those levels with ease. Candy Crush Saga Level 964 Walkthrough Video
lv ransomware|lv ransomware hacked